Call for Abstracts and Participation
Seventh Annual Conference of the Australasian Bayesian Network Modelling Society (ABNMS 2015)
November 23 - 24, 2015: Pre-Conference Tutorials
November 25 - 26, 2015: Conference
Monash University, Caulfield Campus, Melbourne
The organising committee for ABNMS 2015 is pleased to invite the submission of abstracts.
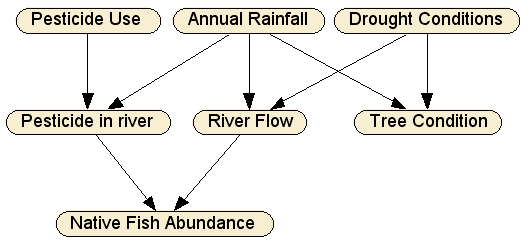
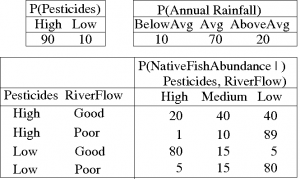
Abstracts are invited from all fields. Past presentations have covered a wide range of disciplines including environmental management, geology, law, ecology and medicine, and a variety of technical aspects on methods of development, data mining, linking GIS with Bayesian Networks, and lessons learned from particular BN projects.
Those beginning to use Bayesian networks are invited to present prospective projects for discussion.
Key Dates
- Call for abstracts: 31 July 2015
- Abstract submission deadline: 4 September 2015
- Decision on abstracts: 11 September 2015
- Deadline for conference registration (including pre-conference tutorials): 21 September 2015
Abstracts for ABNMS 2015 should be no longer than 300 words. Please submit your abstracts via https://www.easychair.org/conferences/?conf=abnms2015
Include the title of your presentation, authors, affiliations, contact details for the corresponding author and abstract. The abstract should be self-contained and explicit, covering the aims, methods, results and main conclusions of the work. The abstract should not contain figures, tables or references.
Travel Grants
The Australasian Bayesian Network Modelling Society (ABNMS) is offering 4 travel grants to attend the ABNMS Tutorials and Conference 23-26 November 2015 Melbourne, Australia. Awards will be for $250 to $500 to contribute to the costs of travel to and from the conference.
Three Student Grants will be awarded and one 2015 Travel Grant for any person who attended the ABNMS pre-conference tutorials in 2014 in Rotorua, New Zealand and will present in 2015.
Applications should include a brief statement indicating the type of travel grant being applied for, justifying the application, an estimate of travel costs, a scanned signed statement from an academic supervisor verifying student status (if in application for one of the student travel grants), and a CV. An abstract of the talk to be presented at the conference must be submitted in parallel (see above). Student travel grants will only be awarded if the recipient registers for the conference and tutorials. Please note the 2015 Travel Grant recipient is not required to register for the pre-conference tutorials.
Travel grant applications must be submitted by email to president@abnms.org by 20 September 2014.
If you have any questions regarding ABNMS2015, please email ABNMS2015@abnms.org.